Introduction to Low Bridge Data and Alerts
Modern fleets live and die by clean map intelligence. If you run box trucks, reefers, or high-cube trailers through older corridors, “know before you go” isn’t optional—it’s compliance. Integrating Low Bridge Data and Alerts into Your Dispatch System turns scattered datasets and vendor tooling into one repeatable workflow: accurate heights, deterministic routing, and real time alerts that hit the driver before a corner’s too late.
Importance in Dispatch Operations
- Route planning with clearance-aware profiles cuts strike risk, detours, and late deliveries.
- Dispatch system integration creates one source of truth for planners, TMS, mobile ELD apps, and yard screens.
- Incident response improves when your alert history is synced to loads, drivers, and proof-of-diligence for insurers.
Challenges in Integration
- Data accuracy: legal vs. physical height, signage vs. measured values.
- Data normalization: meters vs. feet and inches; per-direction clearances; seasonal/temporary works.
- Data latency: long-tail updates (construction) and outage notifications from feeds.
- Cross system interoperability: your TMS, maps SDK, and event bus must agree on IDs, units, and schemas.
Sourcing Low Bridge Data
A robust pipeline blends public data sources, government databases, and commercial data providers, with a clear data governance policy and refresh cadence.
Public Data Sources
- OpenStreetMap (OSM): globally crowdsources legal and physical restrictions. Key tags include maxheight=*, maxheight:physical=*, and maxheight:signed=*. Treat OSM as a baseline—excellent coverage in cities, variable in rural areas—then validate high-risk segments.
- U.S. FHWA National Bridge Inventory (NBI) & LTBP InfoBridge: authoritative bridge records, including vertical clearances (be mindful that some fields address navigation clearances over water rather than roadway). Use as a cross-check for your map layer.
- City & state open data: e.g., NYC Open Data “Citywide Low Bridges” layer and the WSDOT Bridge Vertical Clearance Trip Planner. These provide local precision and metadata (measurement method, directionality).
Commercial Data Providers
- HERE: truck attributes include max permitted height, width, length, axle constraints; routing honors vehicle profiles and can return violated restrictions for audit.
- TomTom: vehicle restrictions APIs and routing parameters (vehicleHeight, vehicleCommercial) to actively avoid low structures when configured.
- GraphHopper / open-source engines: support max_height in custom models and truck profiles (self-hostable, OSM-based). Good for private routing stacks with full control.
Government Databases
- UK (TfL / Ordnance Survey): “Bridges, tunnels, road barriers – height restrictions” (Greater London), released for open use; Network Rail publishes bridge strike statistics and is building a registry of low bridges spanning roads.
- State DOTs: oversize/overweight pre-screening tools and overheight detection specs (e.g., NYSDOT OVDS/LiDAR specs). These are gold for urban infrastructure data and sensor networks that can power proactive alerts.
Practice tip: Treat public/government layers as authoritative context and commercial SDKs as your operational engine. Where they disagree, flag for review, include the source in your data lineage, and prefer the lowest safe clearance until verified.
Utilizing SDKs for Integration
Overview of Available SDKs
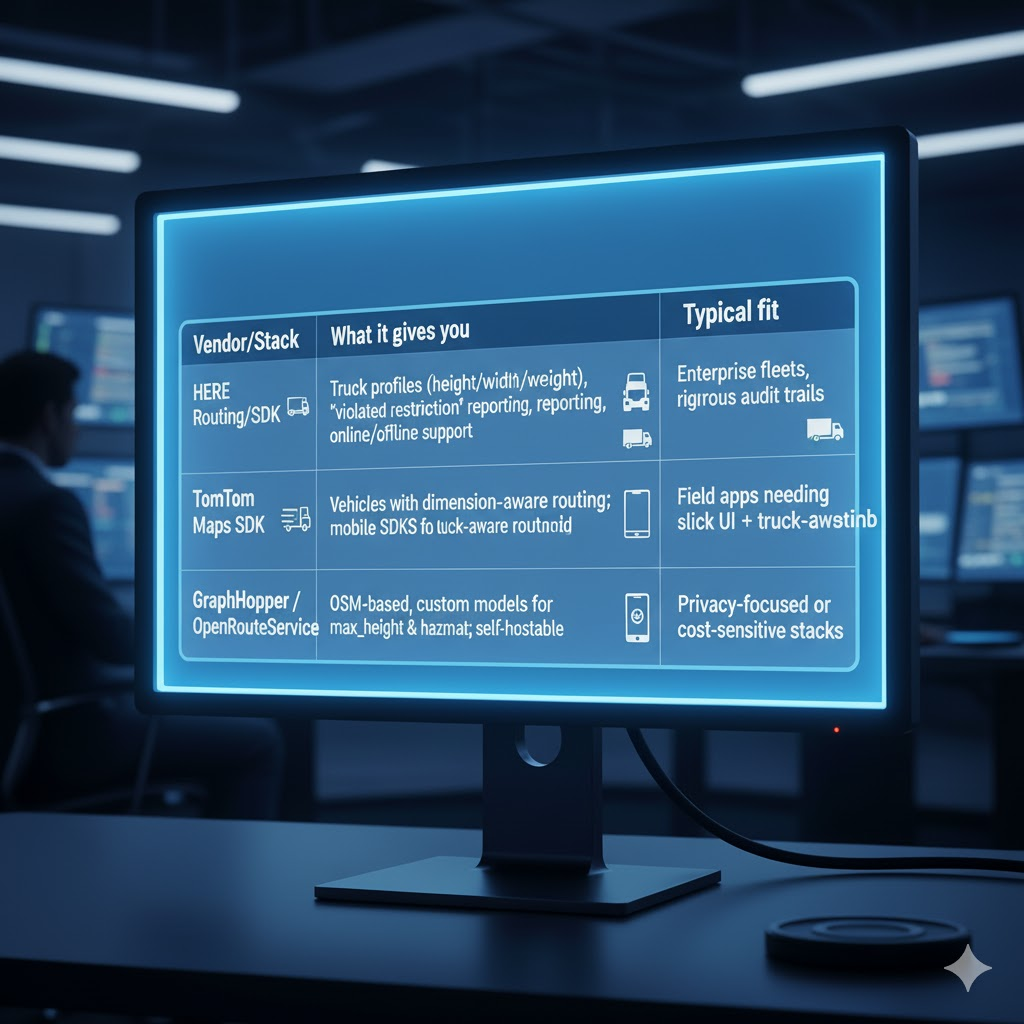
| Vendor/Stack | What it gives you | Typical fit |
| HERE Routing/SDK | Truck profiles (height/width/weight), “violated restriction” reporting, online/offline support | Enterprise fleets, rigorous audit trails. |
| TomTom Routing/Maps SDK | Vehicles with dimension-aware routing; mobile SDKs for iOS/Android | Field apps needing slick UI + truck-aware routing. |
| GraphHopper / OpenRouteService | OSM-based, custom models for max_height & hazmat; self-hostable | Privacy-focused or cost-sensitive stacks. |
Key Features to Consider
- Truck profiles (height/width/weight/axles) and per-trailer presets.
- Offline tiles & fallback routing for dead zones.
- Event hooks: can the SDK return “restriction violated” objects with IDs and geometry? (Great for incident reporting and coaching.)
- API documentation quality, SLAs, and support for fault detection (e.g., when a parameter is ignored, mis-typed, or the map lacks a height tag).
- Data governance: versioned map data, timestamps, and changelogs.
Evaluating SDKs for Compatibility
- Can it ingest your own low bridge overlays (GeoJSON/CSV) on top of the vendor map?
- Unit handling & localization: yards/feet/inches vs. meters; signage conventions.
- Cross system interoperability: web, iOS/Android, and server rendering aligned; uniform route-avoidance rules.
Integrating with Your Dispatch System
Assessing System Requirements
- Where will alerts live? Server-side (pre-dispatch) to avoid bad ETAs or device-side (driver app) for low bridge alerts on approach—or both.
- Latency budget: aim < 2 seconds from new GPS fix to alert; budget for SDK call time + geofence check.
- Ops interfaces: planners need a map view showing clearances, evidence of compliant routing, and “why” a route was changed.
Integration Methods
Pattern A — Server-side clearance gating (pre-dispatch)
- Planner selects a stop sequence.
- Routing microservice builds truck-aware route (SDK vendor or self-hosted).
- Microservice intersects route geometry with your low bridge data sources.
- If conflicts exist, suggest alternates; persist “violated restrictions” in the load record.
Pattern B — Device-side early warning (mobile geofencing)
- App subscribes to GPS; every N meters/seconds, checks a 500–1,000 m corridor ahead against locally cached low-bridge points/polylines.
- If vehicle_height >= clearance_min – buffer, fire escalating warnings (visual + audible) and push an alternate instruction.
Example event payload (webhook → TMS)
{
“event”: “low_bridge_imminent”,
“driver_id”: “DRV-2215”,
“vehicle_id”: “TRK-88”,
“route_id”: “R-10492”,
“timestamp”: “2025-10-20T11:22:13Z”,
“vehicle_profile”: {“height_m”: 4.05, “weight_t”: 36},
“restriction”: {
“id”: “NYC-LB-000112”,
“clearance_m”: 3.85,
“source”: “NYCOpenData”,
“direction”: “NB”,
“last_updated”: “2024-02-10”,
“confidence”: 0.92
},
“position”: {“lat”: 40.7063, “lon”: -73.9427},
“distance_ahead_m”: 430,
“suggested_reroute”: {“eta_delta_min”: 7, “polyline”: “…” }
}
On-device check (pseudocode)
const BUFFER_M = 0.15; // 15 cm safety buffer
if (veh.height_m >= (restriction.clearance_m – BUFFER_M)) {
alertDriver(restriction.id, restriction.distance_ahead_m);
requestReroute(“avoid_restriction”, restriction.geometry);
}
Testing and Validation
- Golden routes: maintain a suite of 50–100 test corridors with known low bridges (e.g., NYC, Boston, London). Cross-check against NYC Low Bridges and TfL datasets.
- SDK parity tests: for each vendor, verify the same vehicle profile avoids identical restrictions; log any violated restriction objects for analysis.
- Field pilots: run side-by-side phones (production vs. beta map data) and measure miss rates, false positives, and data latency.
Best Practices and Considerations
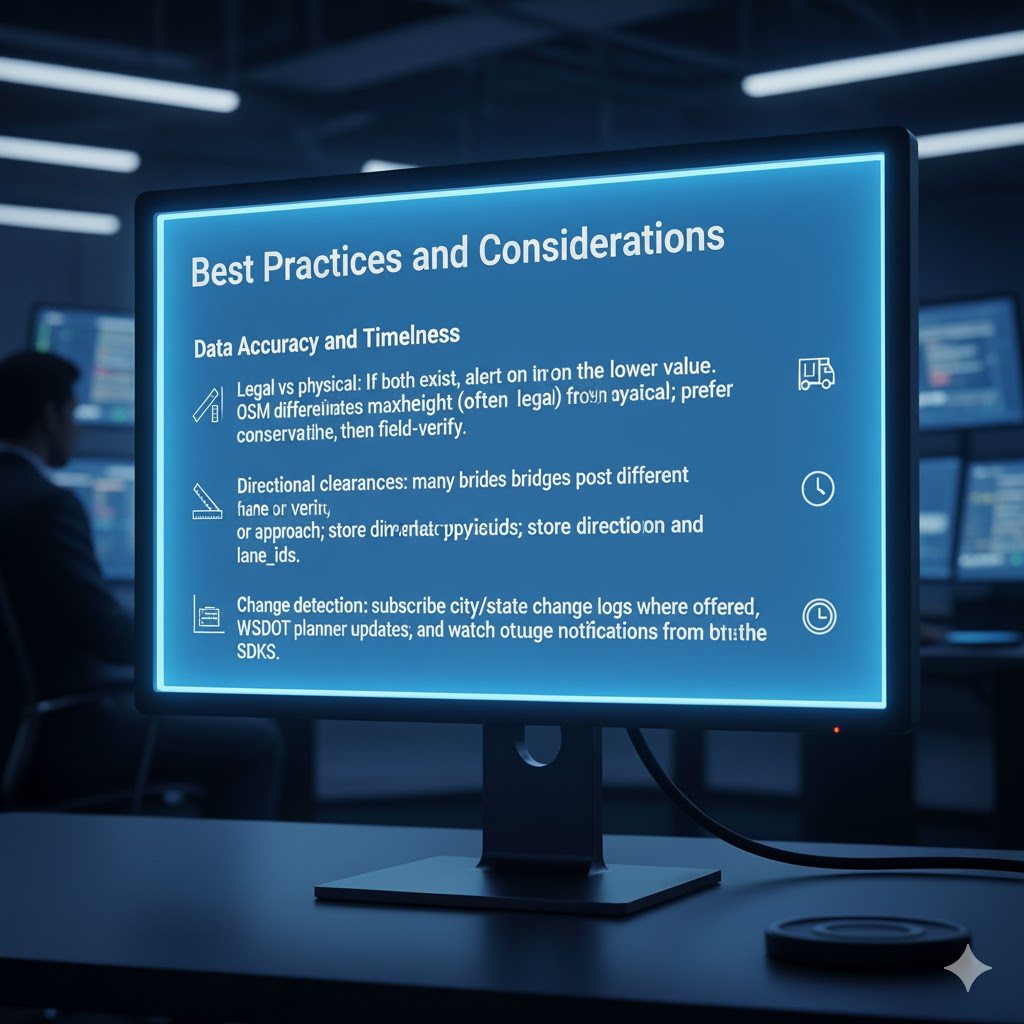
Data Accuracy and Timeliness
- Legal vs physical: If both exist, alert on the lower value. OSM differentiates maxheight (often legal) from maxheight:physical; prefer the conservative one, then field-verify.
- Directional clearances: many bridges post different heights by lane or approach; store direction and lane_ids.
- Change detection: subscribe to city/state change logs where offered (e.g., WSDOT planner updates), and watch outage notifications from SDKs.
Recommended schema (excerpt)
| Field | Type | Notes |
| restriction_id | string | Stable ID across systems |
| geometry | point/segment | WGS-84; include approach bearing |
| clearance_m | float | Minimum verified clearance |
| legal_limit_m | float | If signposted differs from physical |
| direction | enum | NB/SB/EB/WB |
| source | enum | OSM / NYC / TfL / NBI / Vendor |
| measurement_method | enum | survey / signage / sensor |
| confidence | 0–1 | Data quality score |
| last_updated | datetime | For data governance |
| notes | text | Field audit notes / photos |
Scalability and Maintenance
- Tile strategy: cache low-bridge tiles (e.g., 256×256 m GeoJSON shards) near active lanes; purge stale tiles nightly.
- Sensor networks: some DOTs deploy overheight detection (infrared or LiDAR) upstream of problem spans; if the DOT publishes the feed, integrate as a remote parking monitoring–style event stream to preempt strikes.
- Fault detection: alert when data falls below freshness thresholds or when SDK logs show parameter ignores (e.g., height not applied).
- Out-of-band validation: periodically sample against NBI/InfoBridge attributes for drift.
Compliance and Security
- Privacy compliance measures: driver GPS is personal data; rotate IDs, minimize retention, and restrict map replays to investigations.
- Data security standards: TLS, signed payloads, key rotation; segregate the alert bus from public APIs.
- API documentation: publish internal docs that state unit conventions, buffers, and escalation rules (visual, audible, haptic).
- Regulatory defensibility: archive proof of dispatch system integration methods (what data you used, when it was updated, what the driver saw).
Practical Examples & Sources You Can Use Today
Public & Government
- OSM height tags (maxheight, maxheight:physical, maxheight:signed).
- U.S. FHWA NBI / InfoBridge (national bridge records & analytics).
- NYC Open Data “Citywide Low Bridges”; WSDOT Vertical Clearance Trip Planner.
- UK: TfL/OS “Bridges, tunnels, road barriers – height restrictions”; Network Rail bridge strike resources & data products.
Commercial & SDKs
- HERE truck restrictions & violated-restriction reporting.
- TomTom vehicle restrictions and dimension-aware routing parameters.
- GraphHopper custom models for max_height truck routing (self-hosted control).
Sensors & Enforcement Context (for strategy)
- DOT overheight detection specs (NYSDOT infrared & LiDAR examples), WSDOT policies, and weigh-in-motion (NYC DOT on the BQE). These reinforce the case for low bridge alerts paired with policy and enforcement.
Putting It All Together (Reference Architecture)
[Data Ingestion]
├─ OSM diff → normalize units, tags (maxheight*)
├─ City/State feeds (NYC, WSDOT, TfL) → ETL with provenance
└─ Vendor map updates (HERE/TomTom) → SDK version pin
[Governance Layer]
├─ Schema registry (clearance_m, legal_limit_m, direction, confidence)
├─ QA jobs (unit tests + spot surveys)
└─ Change logs + approvals
[Routing + Alerts]
├─ Server routing (trip build, pre-dispatch gating)
├─ Mobile SDK (geofencing, on-device early warning)
└─ Webhooks → TMS (incident reporting & coaching)
[Observability]
├─ Data freshness dashboards (tiles, sources)
├─ SDK health (fault detection, parameter coverage)
└─ Alert KPIs (false positives/negatives, data latency)
Conclusion
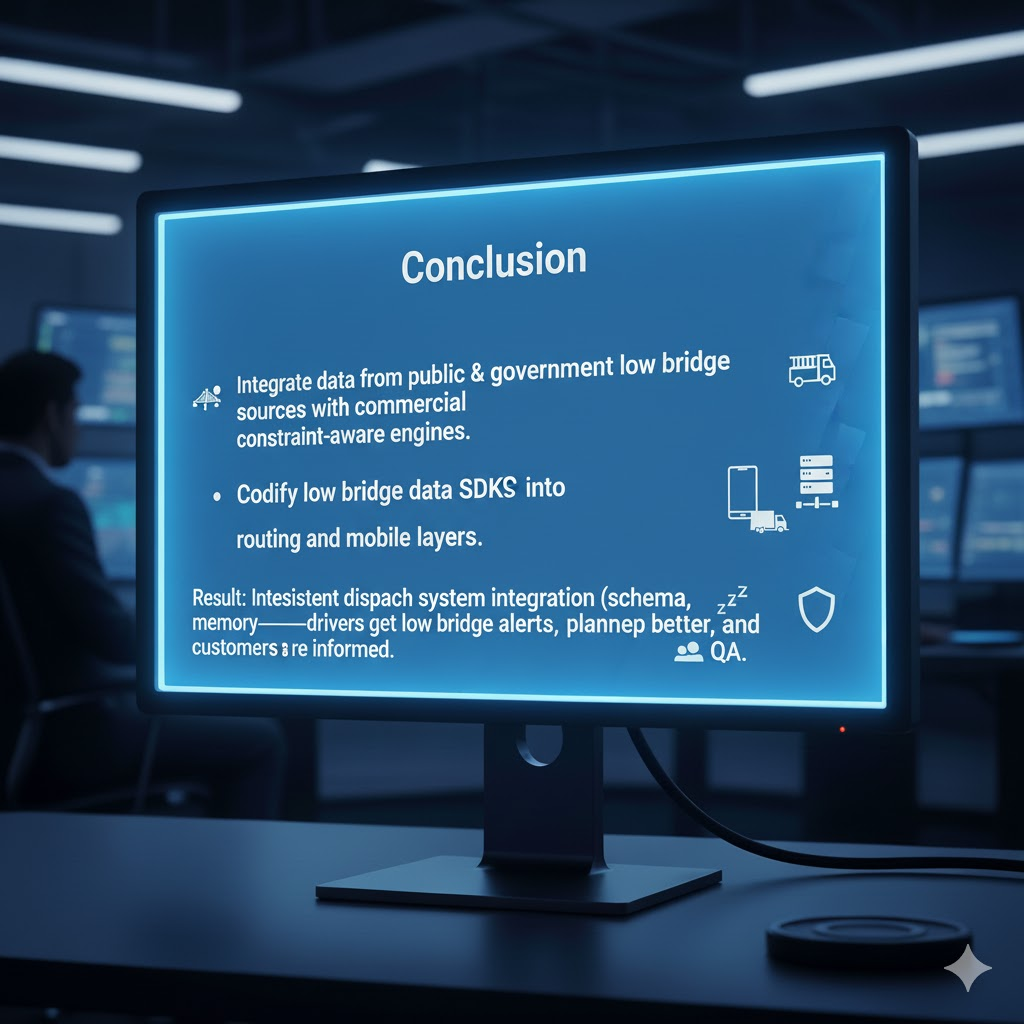
Bridge strikes are costly, reputationally painful, and largely preventable. The winning pattern is simple: marry low bridge data sources from public and government repositories with the mature constraint-aware engines from commercial providers; codify SDKs for low bridge data into your routing and mobile layers; and enforce a boringly consistent dispatch system integration discipline (clear schema, provenance, alerts, and QA). Do this, and Integrating Low Bridge Data and Alerts into Your Dispatch System becomes muscle memory—drivers get low bridge alerts in time, planners sleep better, and customers see fewer “we’re late” emails.
Key takeaways
- Blend OSM + national/city datasets with HERE/TomTom/GraphHopper engines to cover breadth and operational rigor.
- Normalize units, store legal and physical heights, and deploy device-side geofencing for last-mile protection.
- Measure what matters: freshness, alert latency, and true-positive rates—and publish your internal API documentation so everyone plays by the same rules.
With that, you’ve got a practical, scalable playbook for integrating low bridge data—from sourcing and SDK selection to dispatch system integration methods, compliance, security, and continuous improvement across lanes.

 using WordPress and
using WordPress and
No responses yet